Scaling the Fraud Economy: Pig Butchering As a Service

# Massive Magecart Skimming Operation Targets Global Payment Networks Since 2022

Cryptocurrency Crime Skyrockets to $158 Billion Amid Geopolitical Turmoil

Breached Cybercrime Forum's Own Data Exposure Risks Member Identities

Hacktivist Deploys AI Chatbots in Bold Takedown of Neo-Nazi Dating Platforms
Trending_Now
VIEW_ALL_METRICSWorld Economic Forum Sounds Alarm: Deepfake Face-Swaps Pose Critical Threat to Digital Identity Systems
Cisco Issues Critical Patch for Identity Services Engine Flaw Amid Public Exploit Availability
OpenAI Unveils Dedicated Health Chatbot Segment with Rigorous Data Isolation Protections
# ICE's Massive Surveillance Expansion Unveiled: A Domestic Spying Operation Unprecedented in Scale
LIVE_WIRE /// INCOMING_STREAM
Ledger Customer Data Compromised After Third-Party Payment Vendor Global-e Suffers Cyberattack
Inside VVS Stealer: Advanced Obfuscation Techniques Evade Detection
EFF’s Final Year in Review: A Legacy of Long-Term Digital Defense
U.S. Lifts Sanctions on Three Individuals Tied to Intellexa and Predator Spyware Amid Growing Concerns Over Stealth Cyberattacks
RondoDoX Botnet Evolves: Cybercriminals Weaponize Next.js Vulnerabilities in a Multi-Phase Assault Spanning Nine Months
Telegram Breach Exposes Critical Flaws in Session Security: Handala Targets Israeli Officials Amid Wider Cyber Threat Landscape
Cognizant Faces Surge in Class-Action Lawsuits Over TriZetto Data Breach That Lasted Nearly a Year
Boulder’s Atomic Clocks Nearly Collapsed — And the Internet Didn’t Crash
The Cyber War of 2025: How AI, Zero-Days, and Human Trust Shaped the Year’s Most Dangerous Threats
Quick_Briefing
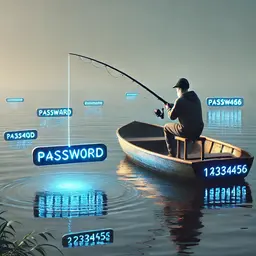
LATEST HEADLINES FROM THE NETWORKThe Rise of AI-Powered Cyber Extortion: How Phishing Gangs Are Evolving Beyond Basic Email Attacks
British Cybercrime Fighter Gavin Webb Honored with OBE for Role in LockBit Takedown
Technology_Frontier
VIEW_ALL_WIRE
Developer Admits Guilty Plea in Landmark Case Against Consumer Spyware Operation

## Critical Audio Codec Flaw Patched in Android’s January 2026 Security Update, Urging User Action

Surging CloudEyE Malware Compromises 100,000+ Systems Globally via Multi-Stage Attacks

UK Unveils Aggressive Cyber Defence Strategy Amid Escalating Digital Threats Targeting Public Services
Latest Wire
Visual_Intelligence
SECURE_CHANNEL_01
DarkSpectre: A 7-Year Long-Game Cyber Campaign Unveiled in Browser Extensions

CSA Warns of Critical SmarterMail Flaw Enabling Unauthenticated Remote Code Execution
Silver Fox APT Exploits India’s Income Tax Trust to Deploy Sophisticated, Stealthy Cyber Campaign
GlassWorm Evolves: A Cross-Platform Cyber Campaign Targets Mac Developers with Hardware Wallet Trojans

US Suspends Backing for Key Cybersecurity Entities Amid Sweeping International Retreat
"# US Suspends Backing for Key Cybersecurity Entities Amid Sweeping International Retreat ## Broad-Based Withdrawal from Multilateral Engagement Pre..."

Global_Conflicts
VIEW_ALL_WIRE
## Government Contractor Subsidiary Breach Confirmed by Sedgwick Amid TridentLocker Ransomware Claims

## Threat Alert: Account Takeover & RCE Flaw in Open WebUI Puts Enterprise AI Deployments at Risk

NordVPN Clarifies Breach Allegations, Citing Exposure of Non-Operational Test Data

European Space Agency Breach Exposes Ongoing Security Challenges in Collaborative Space Research
Editor's Selection
Curated for the informed observer

Trust Wallet Faces Major Supply Chain Breach in Browser Extension Update: A Wake-Up Call for Web3 Security
# Trust Wallet Faces Major Supply Chain Breach in Browser Extension Update: A Wake-Up Call for Web3 Security ## A Critical Flaw in the Supply Chain: How a Leaked API Key Enabled a Malicious Extension Look, this isn’t just another software update gone wrong. This is a serious crack in the foundation of how we trust digital tools in Web3. Trust Wallet just dropped a detailed, work-in-progress update about a major security issue tied to their Browser Extension v2.68 — and it’s not something you can brush off. The breach happened between December 24 and 26, 2025. During that window, a malicious version of the extension — specifically v2.68 — was pushed live to the Chrome Web Store. And here’s the thing: it wasn’t approved through Trust Wallet’s normal internal review process. That’s a red flag from the start. The version that slipped through had backdoor code. It could quietly harvest your wallet details — private keys, balances, transaction history — and even trigger unauthorized transactions without you knowing. Now, that’s scary. But what makes this even worse is where it started. This wasn’t a random hack. It’s directly linked to the *Sha1-Hul

APT36’s Stealthy LNK Campaign: How a Deceptive PDF Shortcut Is Hijacking Indian Government Systems

Hacker Claims Breach of Condé Nast User Database, Threatens Further Leaks

ESA Faces Another Cyber Breach as Hackers Offer 200 GB of Stolen Data for Sale

Cybersecurity Experts Turned Ransomware Operators: How Trusted Skills Were Weaponized Against the Industry
Decode The Signal
Join 50,000+ subscribers. Get our daily intelligence briefing delivered directly to your inbox. No noise, just the critical shifts shaping our future.
SECURE TRANSMISSION. NO SPAM. UNSUBSCRIBE ANYTIME.
Opinion &
Analysis
Expert perspectives on the forces shaping our world. Unfiltered commentary from the frontlines of innovation.
VIEW ALL OPINIONS# Humanized Article:
## Humanized Article: # Rising Recovery Timelines: One-Fifth of Cybersecurity Breaches Need Up to Two Weeks to Fix #...
Unlocking the DHS Spending Trail: Advanced Tactics for Tracking Federal Contracts Through Public Databases
# Unlocking the DHS Spending Trail: Advanced Tactics for Tracking Federal Contracts Through Public Databases ## The T...
## A New Phishing Tactic: Evading Detection with Table-Rendered QR Codes
### A New Phishing Tactic: Evading Detection with Table-Rendered QR Codes --- #### Introduction: The Evolving Scourg...
